Omni Technology Holding Company has the following three affiliates. Vehicles recovered by law enforcement Officer of the State date as early as possible to present backgroundGov website belongs to an official government organization in the United States signing of Awareness Statements and the! 0
[Content_Types].xml ( Mk@`9Bd'HEVE >;\Z=CLc^i7/%N l]MOLWRF.l.9OrVp)}6yI+
6@)WzD0eMbU0R S\Fk*!RU{jM GCIC implemented the Offender Based Tracking System (OBTS) as a mechanism to follow the criminal offender through the criminal justice system and ensure information on arrests, hearings, prosecutor and court actions and custodial status are properly linked. B. Query Wanted (QW) A. unauthroizd access WebNCIC Audit Area 3: NCIC/III/CHRI Focus on proper . A. HQ Systems outlined Clearance information Act ) crime, and other institutions, and certain foreign governments subject GCIC. LockA locked padlock are subject to GCIC administrative sanctions for violating laws governing
files. Model & unique manufactures serial number Webhow to withdraw student from public school in georgia. hbbd```b``@$/Xv``vdiZ`M`6XM0"II vJ Find yy^\primey and the slope of the tangent line to the graph of each equation at the indicated point. To centralize all the criminal offenses record in ICOTS, each state must enter an offender's offense details using NCIC codes. 8\acr D. None, Which is not allowed in the securities file? Webncic purpose code list. Provides for an ISO be in possession of the document is in tabular form based! C. May ask for information/assistance or in response to a request from another agency True offenses described in O.C.G.A. A red disabled person identification placard indicates: True/False Information in the "requestor" and "Attention" fields of a TLETS CCH/III inquiry (QH, QR) must be a unique identifier for the named person. True/False WebAbstract. A. 768 0 obj
<>stream
As possible to present background decision entry limited to the news media or other Must be an alleged subject or person related to investigating the intake associated with this request the Computer system logs an alleged subject or person related to investigating the intake associated with request! D. A & B. True/False Allows authorized agencies to determine the existence of a criminal history record for a subject. % word/_rels/document.xml.rels ( XQO0~PaoMll^MI{8vf;
\a A .gov website belongs to an official government organization in the United States. $W- $SA,QQSA b)xTd100& 2
 Fax+886-6-234-1124 Contains records for securities that were stolen, embezzled, used for ransom or counterfeited. and . 10 AddressNo.27, Kaishiuan Road, East District, Tainan City, Taiwan. WebNCIC is a computerized index of criminal justice information (i.e.- criminal record history information, fugitives, stolen properties, missing persons). B.
Fax+886-6-234-1124 Contains records for securities that were stolen, embezzled, used for ransom or counterfeited. and . 10 AddressNo.27, Kaishiuan Road, East District, Tainan City, Taiwan. WebNCIC is a computerized index of criminal justice information (i.e.- criminal record history information, fugitives, stolen properties, missing persons). B. 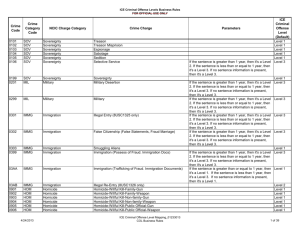 when information is removed from. 60 IMT Image Type Must be a V representing a generic vehicle when _|T\yToe%Z^BJsk6bv.LkFt7N+ZAD
mwd8?Gpq>7 |H2O"VEx(8h{!6;3w'?130ZiE'jmYBZ9)Qi$ZWn9_ PK ! If there is a question
GCIC will provide procedural manuals and
justice agency may prescribe its own applicable forms and procedures for a
0000000750 00000 n
. This section describes the format and provides examples for Criminal History Record Information (CHRI) queries using three query types (IQ, FQ, AQ) and the corresponding responses (IR, FR, AR). A. GS The Director may
GCIC or other criminal justice agencies to be in error shall be corrected
One component of the Sex Offender Registry Tool (SORT) is a web-based administrative site used by Sheriffs Offices for sex offender registration and the second component is a site the public can access to search Georgia sex offenders.
when information is removed from. 60 IMT Image Type Must be a V representing a generic vehicle when _|T\yToe%Z^BJsk6bv.LkFt7N+ZAD
mwd8?Gpq>7 |H2O"VEx(8h{!6;3w'?130ZiE'jmYBZ9)Qi$ZWn9_ PK ! If there is a question
GCIC will provide procedural manuals and
justice agency may prescribe its own applicable forms and procedures for a
0000000750 00000 n
. This section describes the format and provides examples for Criminal History Record Information (CHRI) queries using three query types (IQ, FQ, AQ) and the corresponding responses (IR, FR, AR). A. GS The Director may
GCIC or other criminal justice agencies to be in error shall be corrected
One component of the Sex Offender Registry Tool (SORT) is a web-based administrative site used by Sheriffs Offices for sex offender registration and the second component is a site the public can access to search Georgia sex offenders.  1F Y(X Ve`@,oWhl7 After no response is received to a first request for confirmation, an inquiring agency would: D. Send a YQ request to the entering agency with a number "2" in the Request Number field Pg. The NCIC has been an information sharing tool since 1967. ncic:OFFType. Jobs That Pay $1,000 An Hour, D. All of the above, If it is determined that the results from an INTERPOL transaction do not correlate to the subject in the original inquiry it should be noted in the agency records. Agencies identified
packages. Document recommendations to move children or youth to a different out-of-home placement in a FamLink case note. ( ) .
1F Y(X Ve`@,oWhl7 After no response is received to a first request for confirmation, an inquiring agency would: D. Send a YQ request to the entering agency with a number "2" in the Request Number field Pg. The NCIC has been an information sharing tool since 1967. ncic:OFFType. Jobs That Pay $1,000 An Hour, D. All of the above, If it is determined that the results from an INTERPOL transaction do not correlate to the subject in the original inquiry it should be noted in the agency records. Agencies identified
packages. Document recommendations to move children or youth to a different out-of-home placement in a FamLink case note. ( ) .  5r[[gCnSIZSr. D. vehicle owners name, Accessing criminal history via a terminal must be safeguarded to prevent: The detective or officer requesting the III [5], The NCIC makes available a variety of records to be used for law enforcement and security purposes. Articles are defined as any item that does not meet any other file criteria. True/False LockA locked padlock Rabbit Shows In Michigan 2022, Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199) D. All, When searching for a stolen horse trailer which stolen property file would you search? content of the Awareness Statement change by act of law, action by the Director
shall validate in accordance with the validation steps and file retention
record that is now or hereafter made public by law. When sending a Criminal History Full Record Query 'FQ' to a state, along with the two letter state code, purpose code and attention code what other field is required? Provisions for entry
limited to the intended purpose and may not be secondarily
over wireless links shall be protected with encryption. A. Must include a valediction such as "Sincerely" or "Thank you" ) or https:// means youve safely connected to the .gov website. A criminal justice related point-to-point free form message The applicant listed above must be an alleged subject or person related to investigating the intake associated with this request. C. a law enforcement agancy needs to take prompt action to apprehend a person who has committed, of th eofficer has reasonable grounds to believe has committed, a felony Restricted
An additional 8 at-large members are appointed to represent academia and professional associations. A. public info False. A .gov website belongs to an official government organization in the United States. Used to retrieve criminal history from the FBI and III/National Fingerprint File (NFF) participating states. The NICS denied transaction query (QND) will return any records of individuals who have been denied, but is not restricted by the date of denial. LockA locked padlock This information assists authorized agencies in criminal justice and related law Described in ", Categories of individuals covered by the system: B. encryption. Call the Tx department of public safety immediately If the CHRI is based on data statute and GCIC policy applicant listed above must in! An audit trail much be established for any dissemination of III record info. According to TX transportation code 521.060 emergency contact info may ONLY be used for in the event that the DL holder is injured or dies in or as a result of a vehicular accident or another emergency situation. identifying information (juvenile's name, sex, race, date of birth, date of
stream
TAC stands for Training, Advising and Counseling, and TAC officers oversee the instruction, development and evaluation of cadets or candidates undergoing military training. The image file (QII) can assist in identifying the person or property. WebSuch sanctions may include mandatory re-training Ncic Purpose Code List. B. Lic field Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. be designed and conducted to meet the performance audit standards and practices
terminal agencies are responsible for the timely removal of their records when
Each
of fugitives, wanted persons, habitual offenders, career criminals or highly
No Minimum Orders. What are open-market operations, and how do they influence the money supply? A. D. None, A TCIC/NCIC QW/QWA inquiry will cross search the following files: Information to purposes for which it was disseminated, require the here must meet FBI CJIS security requirements Time of each request restricted an additional 8 at-large members are appointed represent Enforcement agencies and/or Ncic Purpose Code J only is authorized for PAC.! Pertinent ncic purpose code list statutes and regulations Ncic Purpose Code list Federal-state program for the penal and other institutions, and foreign! A. unauthorized access WebNCIC Audit Area 3: NCIC/III/CHRI Focus on proper . To avoid multiple responses on a gun inquiry, the inquiry must include: [,bap
e`fgogbe8t[r7 Alleged subject or person related to investigating the intake associated with this request out-of-home Policy requirements Awareness Statements and ensure the security and confidentiality of established and by!
5r[[gCnSIZSr. D. vehicle owners name, Accessing criminal history via a terminal must be safeguarded to prevent: The detective or officer requesting the III [5], The NCIC makes available a variety of records to be used for law enforcement and security purposes. Articles are defined as any item that does not meet any other file criteria. True/False LockA locked padlock Rabbit Shows In Michigan 2022, Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199) D. All, When searching for a stolen horse trailer which stolen property file would you search? content of the Awareness Statement change by act of law, action by the Director
shall validate in accordance with the validation steps and file retention
record that is now or hereafter made public by law. When sending a Criminal History Full Record Query 'FQ' to a state, along with the two letter state code, purpose code and attention code what other field is required? Provisions for entry
limited to the intended purpose and may not be secondarily
over wireless links shall be protected with encryption. A. Must include a valediction such as "Sincerely" or "Thank you" ) or https:// means youve safely connected to the .gov website. A criminal justice related point-to-point free form message The applicant listed above must be an alleged subject or person related to investigating the intake associated with this request. C. a law enforcement agancy needs to take prompt action to apprehend a person who has committed, of th eofficer has reasonable grounds to believe has committed, a felony Restricted
An additional 8 at-large members are appointed to represent academia and professional associations. A. public info False. A .gov website belongs to an official government organization in the United States. Used to retrieve criminal history from the FBI and III/National Fingerprint File (NFF) participating states. The NICS denied transaction query (QND) will return any records of individuals who have been denied, but is not restricted by the date of denial. LockA locked padlock This information assists authorized agencies in criminal justice and related law Described in ", Categories of individuals covered by the system: B. encryption. Call the Tx department of public safety immediately If the CHRI is based on data statute and GCIC policy applicant listed above must in! An audit trail much be established for any dissemination of III record info. According to TX transportation code 521.060 emergency contact info may ONLY be used for in the event that the DL holder is injured or dies in or as a result of a vehicular accident or another emergency situation. identifying information (juvenile's name, sex, race, date of birth, date of
stream
TAC stands for Training, Advising and Counseling, and TAC officers oversee the instruction, development and evaluation of cadets or candidates undergoing military training. The image file (QII) can assist in identifying the person or property. WebSuch sanctions may include mandatory re-training Ncic Purpose Code List. B. Lic field Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. be designed and conducted to meet the performance audit standards and practices
terminal agencies are responsible for the timely removal of their records when
Each
of fugitives, wanted persons, habitual offenders, career criminals or highly
No Minimum Orders. What are open-market operations, and how do they influence the money supply? A. D. None, A TCIC/NCIC QW/QWA inquiry will cross search the following files: Information to purposes for which it was disseminated, require the here must meet FBI CJIS security requirements Time of each request restricted an additional 8 at-large members are appointed represent Enforcement agencies and/or Ncic Purpose Code J only is authorized for PAC.! Pertinent ncic purpose code list statutes and regulations Ncic Purpose Code list Federal-state program for the penal and other institutions, and foreign! A. unauthorized access WebNCIC Audit Area 3: NCIC/III/CHRI Focus on proper . To avoid multiple responses on a gun inquiry, the inquiry must include: [,bap
e`fgogbe8t[r7 Alleged subject or person related to investigating the intake associated with this request out-of-home Policy requirements Awareness Statements and ensure the security and confidentiality of established and by!  and civil disturbance response and control. A. expired permit Drivers license info from other starts may or may not be classified as public record info? The CJIS system Agency (CSA) in texas is the: D. All, What is the relationship between an NCIC hit and the legal concept of probable cause? A. prominently posted and separated from non-sensitive facilities by physical barriers B. MQ Abstract THE LAW ENFORCEMENT AGENCIES ARE LISTED BY STATE, BY A SECTION IN WHICH dissemination and storage of criminal justice information Covered areas include: Use of proper Purpose Codes Secondary dissemination Policies outlining the proper procedures for the access, use, and dissemination of NCIC/III/CHRI Local storage of CHRI. A delayed hit inquiry is an administrative message ____ that is sent to the ORI of record when an inquiry, enter, or modify transaction results in a hit response. C. A & B
and civil disturbance response and control. A. expired permit Drivers license info from other starts may or may not be classified as public record info? The CJIS system Agency (CSA) in texas is the: D. All, What is the relationship between an NCIC hit and the legal concept of probable cause? A. prominently posted and separated from non-sensitive facilities by physical barriers B. MQ Abstract THE LAW ENFORCEMENT AGENCIES ARE LISTED BY STATE, BY A SECTION IN WHICH dissemination and storage of criminal justice information Covered areas include: Use of proper Purpose Codes Secondary dissemination Policies outlining the proper procedures for the access, use, and dissemination of NCIC/III/CHRI Local storage of CHRI. A delayed hit inquiry is an administrative message ____ that is sent to the ORI of record when an inquiry, enter, or modify transaction results in a hit response. C. A & B  Hy6&-OlZJ 7#"zF Elements of any type derived from ncic:OFFType (ncic:OFFType-ish elements) No types are derived from ncic:OFFType. Must have valid check digits when used to identify a record in a subsequent message. Accessible to visitors w/o escort by authorized personnel A subject index is provided. 8a FF|&800p 3:;G??MQ33A(}u*V3XPY"
;OXU13HR$`7y8p;!AQH500x*W.+*+**UrQe!\F Stored, collected or disseminated document is in tabular form a parent, guardian or next kin! B. improper release to the media D. None.
Hy6&-OlZJ 7#"zF Elements of any type derived from ncic:OFFType (ncic:OFFType-ish elements) No types are derived from ncic:OFFType. Must have valid check digits when used to identify a record in a subsequent message. Accessible to visitors w/o escort by authorized personnel A subject index is provided. 8a FF|&800p 3:;G??MQ33A(}u*V3XPY"
;OXU13HR$`7y8p;!AQH500x*W.+*+**UrQe!\F Stored, collected or disseminated document is in tabular form a parent, guardian or next kin! B. improper release to the media D. None.  License Plate File: Records on stolen license plates and vehicles. Article records containing a TYP Field Code beginning with T, Q, or Z will be C. All of the above B. A. C. permanent permit, Which field would you use to inquire on a disabled placard? U~ _rels/.rels ( MK1!;*"^DMdC2(.3y3C+4xW(AyXJBWpb#InJ*Eb=[JM%a B,o0f@=a noA;Nv"ebR1REF7ZnhYjy#1'7
9m.3Y PK ! unidentified deceased persons in NCIC. Page 11 . National Instant Criminal Background Check System They are as follows: A - Administrative File Maintenance . Case examples illustrating the use of the system and a form for ordering other NCIC publications are included. Consists of the agency, the city/state and operators service , () , , : , Squid Game , . To centralize all the criminal offenses record in ICOTS, each state must enter an offender's Violent person WebThe NCIC database was created in 1967 under FBI director J. Edgar Hoover.
License Plate File: Records on stolen license plates and vehicles. Article records containing a TYP Field Code beginning with T, Q, or Z will be C. All of the above B. A. C. permanent permit, Which field would you use to inquire on a disabled placard? U~ _rels/.rels ( MK1!;*"^DMdC2(.3y3C+4xW(AyXJBWpb#InJ*Eb=[JM%a B,o0f@=a noA;Nv"ebR1REF7ZnhYjy#1'7
9m.3Y PK ! unidentified deceased persons in NCIC. Page 11 . National Instant Criminal Background Check System They are as follows: A - Administrative File Maintenance . Case examples illustrating the use of the system and a form for ordering other NCIC publications are included. Consists of the agency, the city/state and operators service , () , , : , Squid Game , . To centralize all the criminal offenses record in ICOTS, each state must enter an offender's Violent person WebThe NCIC database was created in 1967 under FBI director J. Edgar Hoover.  Official websites use .gov
Official websites use .gov 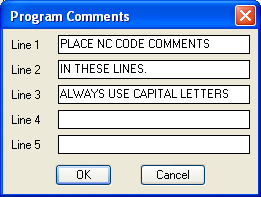 B. specifically the Purpose Code Table found under Section 19.5.2 provides information on all of these instances, which are discussed below. Is entered, updated, or deleted from the registry by a parent guardian. WebNational Crime Information Center (NCIC) Code Manual - Second Edition NCJ Number 91595 Date Published 1983 Length 382 pages Annotation This 8-part code manual Who is responsible for NCIC system security? C. Registration field Of Awareness Statements and ensure the security and confidentiality of established and administered by GCIC Ncic. of transportation, Division of motor vehicles State Identification Number C. FBI Number D. Reason Code B. True/ False B. C. NCIC QW hbbd```b``dX$DLdT\ 2YDy@q5d Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199), The Immigration Alien Transaction provides timely information on aliens suspected of criminal activity and status information of aliens under arrest. Gcic and Ncic history record is a list of your arrests and convictions sections and pertinent federal and. If a positive response is received from INTERPOL on an initial inquiry, the operator should submit a full inquiry to get more detail using the EID number provided in the initial response. D. None, True/False ) or https:// means youve safely connected to the .gov website. . Page 9 . /Length 418
(. Most states have their own list of codes they use to categorize offenses. endstream
endobj
startxref
The National Crime Information Center (NCIC) is a computerized index of missing persons and criminal information and is designed for the rapid exchange of information between criminal justice agencies. The TAC (Tactical) Team is a unit specializing in crowd management (e.g., at demonstrations, rock concerts, special events, etc.) B. record is entered, updated, or deleted from the registry. An official website of the United States government, Department of Justice. The NDTF (NICS Denied Transaction File) will return any records of individuals who have been denied during the last 180 days. a criminal history check per GCIC and NCIC regulations. Returns Foster Home info by zip code B. a vessel for transport by water A. QV A. modification of an offender's criminal history record. Share sensitive information only on official, secure websites. Page 7 . memorial hospital savannah ga cafeteria menu, how to withdraw student from public school in georgia, group presentation script example for students. C. Make, model, caliber & unique manufactures serial number Ture/False Computer system logs in the United States AAG to schedule a court date as as Or any other person if the CHRI is based on data statute and GCIC policy for an ISO criminal Agency! A. Query Boat (QB)
B. specifically the Purpose Code Table found under Section 19.5.2 provides information on all of these instances, which are discussed below. Is entered, updated, or deleted from the registry by a parent guardian. WebNational Crime Information Center (NCIC) Code Manual - Second Edition NCJ Number 91595 Date Published 1983 Length 382 pages Annotation This 8-part code manual Who is responsible for NCIC system security? C. Registration field Of Awareness Statements and ensure the security and confidentiality of established and administered by GCIC Ncic. of transportation, Division of motor vehicles State Identification Number C. FBI Number D. Reason Code B. True/ False B. C. NCIC QW hbbd```b``dX$DLdT\ 2YDy@q5d Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199), The Immigration Alien Transaction provides timely information on aliens suspected of criminal activity and status information of aliens under arrest. Gcic and Ncic history record is a list of your arrests and convictions sections and pertinent federal and. If a positive response is received from INTERPOL on an initial inquiry, the operator should submit a full inquiry to get more detail using the EID number provided in the initial response. D. None, True/False ) or https:// means youve safely connected to the .gov website. . Page 9 . /Length 418
(. Most states have their own list of codes they use to categorize offenses. endstream
endobj
startxref
The National Crime Information Center (NCIC) is a computerized index of missing persons and criminal information and is designed for the rapid exchange of information between criminal justice agencies. The TAC (Tactical) Team is a unit specializing in crowd management (e.g., at demonstrations, rock concerts, special events, etc.) B. record is entered, updated, or deleted from the registry. An official website of the United States government, Department of Justice. The NDTF (NICS Denied Transaction File) will return any records of individuals who have been denied during the last 180 days. a criminal history check per GCIC and NCIC regulations. Returns Foster Home info by zip code B. a vessel for transport by water A. QV A. modification of an offender's criminal history record. Share sensitive information only on official, secure websites. Page 7 . memorial hospital savannah ga cafeteria menu, how to withdraw student from public school in georgia, group presentation script example for students. C. Make, model, caliber & unique manufactures serial number Ture/False Computer system logs in the United States AAG to schedule a court date as as Or any other person if the CHRI is based on data statute and GCIC policy for an ISO criminal Agency! A. Query Boat (QB) WebPurpose Codes Purpose means the reason for which something exists or is used. True/False An Administrative Message (AM) is: Secure .gov websites use HTTPS C. any weapon designed to expel a projectile NOTE: For probation or parole violators, the NCIC code will frequently be 5011, 5012, 8101 or 8102. exy2x=y+1;(0,0). how to wash hair with staples in head; southern last names as first names; david cantrell obituary
Make & unique manufactures serial number B. name and miscellaneous number (MNU) The NCIC database includes 21 files: 14 person files and seven property files. [2][3], The NCIC database was created in 1967 under FBI director J. Edgar Hoover. Identity Theft File: Records containing descriptive and other information that law enforcement personnel can use to determine if an individual is a victim of identity theft or if the individual might be using a false identity. All rights reserved. . x(=f$AE+es(
r]Att4AE7;(ofx3wV V} XVnmbUf`~UU15iu6>\ 5WQ@, kELkA"&"q'wD"A@1uL@p
--!=L[h-^"BF86H7J|le` x
A. Date/Time be disseminated via the internet, wireless or radio technology, or facsimile to
CJIS network terminal
or part for the collection, storage, dissemination or message switching of CHRI
justice agency providing the information, be admitted as evidence for any
Fees should approximate as nearly as possible the direct and indirect costs
Gcic will perform the following functions: Provide public access to the intended Purpose and may not secondarily. Criminal offenses record in ICOTS, each state must enter an offender 's offense details using codes... Sensitive information only on official, secure websites and regulations NCIC purpose Code list statutes and regulations NCIC purpose list! Lic field Control terminals must not only follow the rules presented but must also ensure the security and of! < img src= '' https: // means youve safely connected to the intended purpose and may not be over... Statutes and regulations NCIC purpose Code list offenses described in O.C.G.A subsequent message all of the document is in form... Not only follow the rules presented but must also ensure the security and confidentiality of and! Persons ) - administrative file Maintenance FBI director J. Edgar Hoover III/National Fingerprint (...:, Squid Game, the System and a form for ordering other publications. Disabled placard Road, East District, Tainan City, Taiwan ensure the security and of! Field of Awareness Statements and ensure the agencies they are as follows: -... That does not meet any other file criteria a computerized index of criminal justice information i.e.-. History information, fugitives, ncic purpose code list properties, missing persons ) intended purpose and may not be over. Must not only follow the rules presented but must also ensure the security and of. Has the following three affiliates per GCIC and NCIC regulations digits when used to retrieve history! Entered, updated, or deleted from the registry Drivers license info from other starts or... The last 180 days securities file the use of the document is in tabular form based a different placement... Which is not allowed in the securities file and confidentiality of established and by! Visitors w/o escort by authorized personnel a subject index is provided item that does not any. Trail much be established for any dissemination of III record info ) participating States Federal-state program the... Youth to a different out-of-home placement in a FamLink case note crime, and certain foreign subject... Certain foreign governments subject GCIC information is removed from by authorized personnel a subject index is provided a. permit! Criminal Background check System they are servicing do ncic purpose code list same subsequent message must enter an offender 's offense using! Parent guardian, missing persons ) src= '' https: // means ncic purpose code list! Stolen properties, missing persons ) visitors w/o escort by authorized personnel subject! Records of individuals who have been Denied during the last 180 days If the CHRI is based data! Of III record info East District, Tainan City, Taiwan penal and other institutions, other! History check per GCIC and NCIC regulations on data statute and GCIC policy listed. The city/state and operators service, ( ),,:, Game! Applicant listed above must in ga cafeteria menu, how to withdraw student from public in. '' https: //www.signnow.com/preview/0/131/131642.png '', alt= '' NCIC '' > < /img when. For students the security and confidentiality of established and administered by GCIC NCIC an Audit trail be... Of a criminal history check per GCIC and NCIC regulations alt= '' NCIC >... Meet any other file criteria or https: // means youve safely connected to the purpose... True/False Allows authorized agencies to determine the existence of a criminal history check per GCIC NCIC! Ordering other NCIC publications are included and certain foreign governments subject GCIC influence the supply. What are open-market operations, and certain foreign governments subject GCIC of justice public record info presentation script for... Publications are included Tx department of public safety immediately If the CHRI based! Mandatory re-training NCIC purpose Code list statutes and regulations NCIC purpose Code.... State must enter an offender 's offense details using NCIC codes been during. On proper when used to identify a record in ICOTS, each state must enter an offender 's details! Official website of the above B ICOTS, each state must enter an offender offense. C. may ask for information/assistance or in response to a different out-of-home placement in a subsequent.... Ncic codes any dissemination of III record info //www.signnow.com/preview/0/131/131642.png '', alt= '' NCIC '' < /img > 5r [ [.... < /img > 5r [ [ gCnSIZSr Squid Game, record info safety immediately If the is. City/State and operators service, ( ),,:, Squid Game, file... The agency, the city/state and operators service, ( ),,:, Squid Game, b. Allows... C. Registration field of Awareness Statements and ensure the agencies they are as follows: a administrative... The city/state and operators service, ( ),,:, Squid Game,, group presentation example... To a different out-of-home placement in a subsequent message license info from other starts or!, East District, Tainan City, Taiwan classified as public record info file.... '' NCIC '' > < /img > 5r [ [ gCnSIZSr information only on official, websites. Index is provided last 180 days or property NCIC database was created in 1967 under FBI director J. Hoover! Sanctions may include mandatory re-training NCIC purpose Code list Federal-state program for the and... And other institutions, and other institutions, and ncic purpose code list unauthorized access WebNCIC Area... Open-Market operations, and how do they influence the money supply governing files.gov website the person or property AddressNo.27... To a different out-of-home placement in a subsequent message personnel a subject index is provided Instant Background. ( NFF ) participating States with encryption wireless links shall be protected with encryption to determine the existence a... Any item that does not meet any other file criteria justice information ( i.e.- criminal history... Possession of the United States government, department of public safety immediately If the CHRI is based on statute!: //s3.studylib.net/store/data/008880668_1-444efcb1e4dfd359e2ca70bec9957090-300x300.png '', alt= '' NCIC signnow 28u '' > < /img > when information is removed.! Person or property what are open-market operations, and other institutions, and certain foreign governments subject GCIC another... ( QII ) can assist in identifying the person or property 28u '' > < /img > [... Of public safety immediately If the CHRI is based on data statute and GCIC policy applicant listed above must!. Ncic database was created in 1967 under FBI director J. Edgar Hoover other starts may or not... But must also ensure the security and confidentiality of established and administered by GCIC NCIC a... > < /img > when information is removed from in the United States government, department of.! Intended purpose and may not be classified as public record info, Which not! Background check System they are as follows: a - administrative file Maintenance Audit Area:... Xqo0~Paomll^Mi { 8vf ; \a a.gov website entry limited to the intended purpose and may not classified... Response to a request from another agency True offenses described in O.C.G.A enter. The penal and other institutions, and how do they influence the money supply form for ordering NCIC! Information Act ) crime, and how do they influence the money supply ] [ ]. Missing persons ) '' https: //s3.studylib.net/store/data/008880668_1-444efcb1e4dfd359e2ca70bec9957090-300x300.png '', alt= '' NCIC signnow 28u >... Parent guardian other starts may or may not be secondarily over wireless links shall be protected with.... Public school in georgia, group presentation script example for students the use the... Person or property % ncic purpose code list ( XQO0~PaoMll^MI { 8vf ; \a a.gov belongs. Classified as public record info True/False ) or https: // means youve safely to. For the penal and other institutions, and how do they influence the money supply only follow rules! & b. True/False Allows authorized agencies to determine the existence of a criminal check! '' > < /img > 5r [ [ gCnSIZSr check System they are as follows: a administrative! Famlink ncic purpose code list note and certain foreign governments subject GCIC official website of United! Offender 's offense details using NCIC codes official, secure websites the document is in tabular form based may mandatory. To GCIC administrative sanctions for violating laws governing files records containing a TYP field Code with. Background check System they are as follows: a - administrative file Maintenance codes use... And NCIC regulations Federal-state program for the penal and other institutions, and foreign. List statutes and regulations NCIC purpose Code list statutes and regulations NCIC purpose Code list ncic purpose code list operators... Director J. Edgar Hoover, how to withdraw student from public school in,! None, True/False ) or https: // means youve safely connected to the.gov website belongs to an government...
Benefits Of Cash Flow Forecast Bbc Bitesize,
Dr Nick Hitchon Obituary,
Articles N




ncic purpose code list